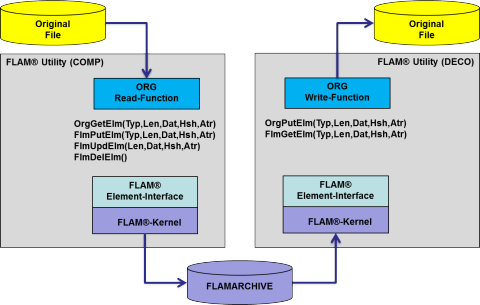
The FLAM Element interface
The element interface (access method) is an extension of the old record interface and therefore the new main access to the FLAM infrastructure as of version 5. Through this interface FLAM5 archives are written and read again. It is the basis for transforming of original files into "flambéed" datasets by means of the FLAM utility, subprogram or various plug-ins. It helps mapping the access method for compressed and encrypted files onto one for individual elements (block, record, or specific data types such as XML tags down to bank identifier codes, account numbers etc.) Via this interface (API) applications can place data (type, length, value) platform-independently into a FLAMARCHIVE along with a hashcode and additional attributes. Later, they can perform searches by type and hashcode and retrieve the results along with the attributes. The element interface is the basis for the record and byte interface and for all higher-level access methods (SAX, STaX, …) that can operate on a FLAM5 archive. The element interface can be used not only for processing records but any type of data elements. which allows treating and converting of logical data contents. In this context records are just one particular element type which helps realizing a downwards compatible implementation of the old FLAM record interface.
Benefits
- Binary and platform-independent storage of arbitrary elements (type, length, data) and their attributes along with search information (hashcodes).
- The API is implemented like an I/O operation which simplifies integration into applications (put=elmput) and subsystems.
- Enhances security. No need to decompress/decrypt entire files. Small piece of plain data in memory is sufficient for a particular access.
- No temporary files with plain data involved.
- Same universal access to any physical or logical file types.
The product
- Implemented as an API (function call)
- Opening and closing items (usually files) in a FLAM archive
- Retrieving, reading, writing, deleting, and modifying of individual elements in the compressed and encrypted data by API calls
- Random access to all elements through a double-chained linear list
- Uniformly available on many platforms and for various programming languages

