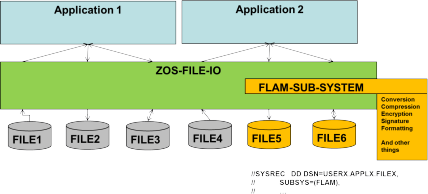
FLAM Subsystem
The FLAM subsystem uses the FLAM record interface on the host computer to let a compressed an encrypted FLAMFILE appear as the original file - transparently for the applications. It does that by installing itself as a system driver /service provider in the operating system, intercepting the applications' data accesses, and mapping them against the FLAMFILE without the applications noticing this. By means of the FLAM utility such original files can be transformed to FLAMFILEs during migration, or FLAMFILEs created with the subsystem can be recovered as original files. If this is done while applying the key for the data recipient via the FLAM key-management extension (FKME), then by the time the data are written both security requirements, regarding storage (Data at Rest) and transport (Data in Transit), have been satisfied in one stroke without any changes to the application. As an example, LOG files can finally be written in compliance with most recent security standards. The FLAM subsystem is available under z/OS for all record-oriented file types including VSAM.
Benefits
- Any host file types can be compressed and encrypted - transparently to the application.
- With that, all access methods of the original file remain available, so applications are not aware of this additional protection.
- Due to compression less file I/O is induced leading to shorter run times and better response times.
- The integration is done in JCL, programs need not be changed.
- This is true for all applications irrespective of their programming language (COBOL, JAVA, C, PL/1, C++, Assembler, …).
- Fully compatible with the FLAM utility. FLAMFILEs are mutually interchangable.
The product
- Implemented as a z/OS-subsystem, hence no program changes required
- FLAM® runs as Started Task in the background
- Activated via JCL (DD-statement)
- Transparent read/write of data records in compressed/encrypted FLAMFILEs of any type
- Additional find/change/delete/insert in VSAM-KSDS-FLAMFILEs via key of original record on record level
Quotation of the developer
"The capabilities of FLAM as an access method are impressively demonstrated by its implementation as a subsystem. By that, data accesses done by an application or a utility are redirected to FLAM accesses - invisibly for the originator. Files remain compressed and encrypted. For an access, just small segments must be converted to plain data, not the entire file. Changes in existing programs are not necessary."

