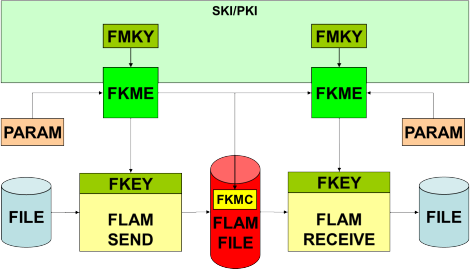
FLAM Key-Management Extension
The FLAM key-management extension (FKME) links between FLAM's cryptographic protection mechanisms (privacy, integrity, completeness), various cryptographic infrastructures (KMIP, x509-PKI, FINPIN, …), and various architectures of hardware security modules (HSM (IBM-CCA/ICSF, PKCS#11, ...)) in order to provide a professional key management by which access to data can be controlled. Of course, FLAM also supports protection by a simple passsphrase or an internal constant as keys, but professional solutions are implemented by means of this service-provider interface which has been available since FLAM version 4.
Benefits
- Use of existing cryptographic infrastructures for protecting "flambéed" data
- Processes for key management and permission granting can be re-used
- Top security due to support of various hardware security modules (HSM)
- No downstream costs caused by encryption
- Compliance with security requirements and standards
The product
- Easy integration of FLAM® into existing cryptographic infrastructures (SKI (FINPIN) oder PKI (KIMP, PGP, x509 (SSL))) via a standardized service provider interface (SPI) for providing and protecting key materials
- Off-the-shelf or inhouse solutions may be deployed
- FKME can be implemented against various sorts and architectures of hardware security modules. Thus, compatibility across heterogeneous hadware can be established
- Re-keying the data key of a FLAMFILE® enables, for one thing, controlling access to the data but also carrying out sporadic or periodic key exchange and securely organizing central headends, archives, and mediators.
- Access capability to individual data elements (records) is fully preserved
- Reference software implementations exist for the different solutions to allow testing and for quick starts into projects
Our added value
- Proven security, cryptography, Hardware-Security-Module (HSM), and key management are core competencies of our enterprise.
- Compliance with security requirements (such as PCIDSS), secure clouding and oursourcing, as well as professional key management were in the focus of the development.
- Searches within encrypted and compressed data sets with access to individual data elements (without decrypting files entirely) is being combined with strict protection of data elements (Need to know).
Implementations
FKME can be used as an SPI for connecting various cryptographic infrastructures. The following FLAM4-based solutions are currently available:
- FIN/PIN for PCIDSS: for secure ordering of debit and credit cards a specification was developed that relies on the existing cryptographic infrastructure for the Financial-PIN-Support. For this, there are meanwhile two different specifications: one for triple-DES and also one for AES which exists in two versions (transfer and storage). Beside a reference software implementation we are offering one for PKCS#11 and IBM-CCA-based HSM for all platforms.
- AES-based solution for secure storage of database unload, the IMS log, dumps and other critical data via our subsystem on host computers, which works similarly to the DB2/IMS database encryption tool of IBM and which can be used with the same protected key over the ICSF.
The following FKME are planned as part of the FLAM5 project:
- Connecting the x509-PKI, so that the same infrastructure can be used for FLAM as that already deployed with many enterprises for SSL/TLS servers.
- KMIP (Key-Management-Interoperability-Protocol) support, so that a central EKM (Encryption Key Manager) can be used for protecting "flambéed" data.
In various other projects customers have developed their own specifications and implemented their own solutions.

